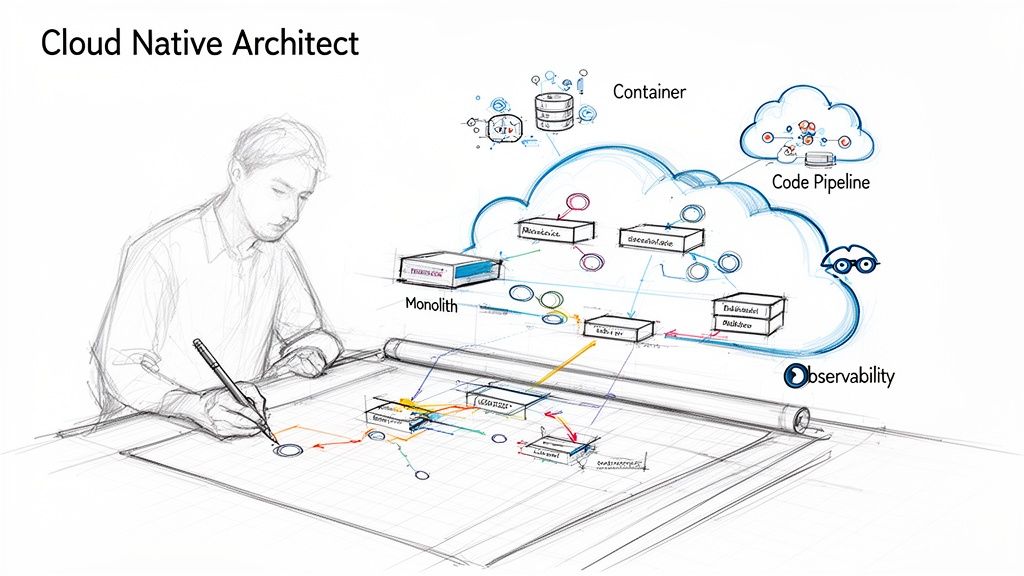
A cloud native architect is the master planner behind modern, distributed software systems. They don't just migrate applications to the cloud; they design them to be born in the cloud, creating the technical blueprints for systems that are resilient, scalable, and engineered for high-velocity development.
The Strategic Role of the Cloud Native Architect

Here's a hard truth: simply running monolithic applications on cloud virtual machines is a legacy strategy. The real competitive advantage comes from architecting applications for the cloud from the ground up, leveraging its unique capabilities. This is the core mindset a cloud native architect brings to the table.
A traditional architect might design a sprawling, single-structure mansion where every room is tightly connected. If the foundation cracks, the entire house is compromised. That’s a monolithic application—powerful, but rigid and fragile, with a large blast radius for failures.
A cloud native architect, on the other hand, designs a modern metropolis of independent structures (microservices), all connected by a robust grid of communication protocols and infrastructure (APIs, service meshes, and event buses). If one building has a plumbing issue, it is isolated, and the rest of the city continues to function without interruption.
This isn’t just a technical shift; it’s a strategic one. Businesses are catching on, which is why the cloud native development market is set to jump from $1,087.96 billion in 2025 to an incredible $1,346.76 billion in 2026. That's a 23.8% growth rate in a single year, as highlighted in a report by The Business Research Company.
A New Blueprint for Software
The cloud native architect's job is to define the technical strategy for this modern software "city." They make the high-level design choices—like defining service boundaries, selecting communication patterns, and establishing data consistency models—that determine whether a system can adapt to change, survive outages, and scale efficiently, directly tying technical decisions to business outcomes.
A cloud native architect translates business goals into an architectural vision that squeezes every last drop of potential out of the cloud. They plan for change, expect failure, and design for massive scale from day one.
This technical approach delivers tangible business results:
- Faster Time-to-Market: With independent services, teams can develop, test, and deploy features on autonomous release schedules, eliminating the bottlenecks of monolithic release cycles.
- Enhanced Resilience: The system is designed for failure. When one microservice fails, its impact is contained, and the rest of the application remains available, often through graceful degradation.
- Cost-Efficient Scalability: You can scale individual services based on real-time demand (e.g., scaling the
checkout-serviceduring a sale), ensuring you only pay for the precise resources you need.
The table below provides a technical comparison of this paradigm against traditional monolithic architecture. It's a fundamental shift in software engineering principles.
Traditional vs Cloud Native Architecture At A Glance
| Aspect | Traditional Architect | Cloud Native Architect |
|---|---|---|
| Application Design | Monolithic; tightly coupled components with a single database schema. | Microservices; loosely coupled, single-responsibility services with independent data stores. |
| Deployment Unit | The entire application at once, leading to high-risk, infrequent deployments. | Individual services or containers, enabling low-risk, frequent deployments. |
| Infrastructure | Static servers, often provisioned and configured manually. | Dynamic, ephemeral infrastructure defined as code (IaC) and managed via APIs. |
| Scalability | Scale the entire monolith vertically (more CPU/RAM) or horizontally (more instances). | Scale individual services horizontally based on specific metrics (e.g., CPU, queue length). |
| Failure Response | Application-wide outage from a single component failure. | Graceful degradation; localized impact, often with automated self-healing. |
Ultimately, a cloud native architect champions this new model, moving the organization from a rigid and fragile state to one that is agile, resilient, and ready for whatever comes next.
Core Technical Responsibilities of a Cloud Native Architect
A Cloud Native Architect doesn't just produce diagrams and whitepapers. Their work happens at the intersection of code, infrastructure, and strategy, turning architectural blueprints into living, breathing systems. This requires making critical, hands-on technical decisions that define how software is built, deployed, and operated.
Their responsibilities consolidate into four key technical domains. Deep expertise in these areas is what distinguishes a true architect from a senior developer.
Designing Scalable Microservices
The first responsibility is often decomposing monolithic systems into a set of smaller, independent microservices. This is a complex exercise in domain-driven design, not just code refactoring.
An architect must define clear service boundaries based on business capabilities. For an e-commerce platform, this means creating distinct services for user-accounts, product-catalog, shopping-cart, and payments. This logical separation allows the payments team to deploy a PCI-compliant update without impacting the product search functionality.
A critical design decision is defining inter-service communication patterns. Should services use synchronous REST/gRPC calls for immediate responses, or an asynchronous, event-driven approach with a message broker like RabbitMQ for resilience and decoupling? The architect makes this call, weighing trade-offs between latency, consistency, and operational complexity for each interaction.
Automating Infrastructure with IaC
A Cloud Native Architect operates on the principle that manual infrastructure changes are a source of instability and error. The goal is to create environments that are 100% automated, version-controlled, and immutable. This is achieved through Infrastructure as Code (IaC).
Using tools like Terraform or Pulumi, every component—VPCs, subnets, Kubernetes clusters, IAM roles, databases—is defined in declarative code files stored in a Git repository. Need a new staging environment? Run a script. This eliminates configuration drift and turns disaster recovery from a high-stress incident into a predictable, automated process.
Imagine a primary cloud region goes offline. The legacy approach involves a frantic, all-hands scramble to manually rebuild infrastructure in a backup region. With a mature IaC strategy, the architect has already codified the entire environment. The recovery procedure is to execute a pre-tested script against the secondary region, restoring full service in minutes, not days.
Engineering Elite CI/CD Pipelines
A well-designed architecture is useless without a secure, high-velocity path to production. The architect designs the Continuous Integration and Continuous Deployment (CI/CD) pipelines—the automated assembly lines that move code from a developer's IDE to a production environment.
This is far more than a simple build-test-deploy script. A modern, cloud native pipeline is a sophisticated system with automated guardrails, often implemented using GitOps principles. It must include:
- Automated Security Scanning: Static Application Security Testing (SAST), Dynamic Application Security Testing (DAST), and container image scanning (e.g., with Trivy or Snyk) to catch vulnerabilities before they reach production.
- Progressive Delivery Strategies: Implementing canary releases or blue-green deployments using service meshes (like Istio) or ingress controllers to roll out changes to a small subset of users, minimizing the "blast radius" of a failed deployment.
- Automated Rollbacks: If key Service Level Indicators (SLIs) like error rate or latency degrade past a defined threshold post-deployment, the pipeline must automatically trigger a rollback to the last known good version.
By engineering these automated safety mechanisms, the architect empowers development teams to deploy multiple times per day with high confidence.
Implementing Deep Observability
Finally, you cannot operate what you cannot observe. The architect is responsible for ensuring systems are deeply observable. This is a significant evolution from traditional monitoring, which answers "is the server up?" Observability provides the data to answer "why is the system behaving this way?"
This is achieved by instrumenting every layer of the stack to produce three essential data types (the "three pillars"):
- Metrics: Time-series numerical data (e.g., request latency, CPU utilization) that provides a high-level view of system health, typically stored in a time-series database like Prometheus.
- Logs: Granular, time-stamped records of discrete events (e.g., an application error, a user login) that provide rich, contextual detail for debugging.
- Traces: An end-to-end representation of a single request's journey as it propagates through multiple microservices, essential for pinpointing latency bottlenecks in a distributed system.
By correlating these signals in a platform like Grafana or Datadog, an engineering team can diagnose a vague "the site is slow" alert down to a specific, inefficient database query in a downstream service. This level of insight is non-negotiable for operating complex systems.
The Essential Technical Toolkit for Cloud Native Architects
An effective cloud native architect is defined by their hands-on mastery of the tools that build, run, and secure modern distributed systems. This is not a random list of buzzwords, but a curated ecosystem of technologies where each component solves a specific architectural problem.
This tool-centric approach is what fuels the market's explosive growth, with projections of a 24.10% CAGR for the cloud native market from 2025 to 2033. This boom is driven by the industry-wide adoption of containerization and microservices, where Kubernetes has become the de facto control plane for the cloud.
The flowchart below illustrates the cyclical relationship between these core responsibilities.

The process is iterative: design with microservices, automate with IaC and CI/CD, and gather feedback through observability to inform the next design iteration. Mastering this loop is the job.
Containerization and Orchestration
This is the foundational layer of any cloud native stack. Applications are packaged into containers, and an orchestrator manages their lifecycle.
Docker: The tool for packaging an application with its dependencies (libraries, runtime, config files) into a standardized, portable container image. For an architect, Docker ensures environmental consistency, eliminating the "it works on my machine" problem by providing a uniform artifact for development, testing, and production.
Kubernetes (K8s): The orchestrator that manages the deployment, scaling, and self-healing of containerized applications. An architect leverages Kubernetes primitives (Deployments, StatefulSets, Services) to build systems that automatically recover from failures, scale on demand, and manage complex network policies. It has become the operating system for the cloud.
Infrastructure as Code
A cloud native architect never uses a cloud provider's web console for provisioning. Every virtual machine, database, and firewall rule is defined as version-controlled code.
Infrastructure as Code (IaC) is a non-negotiable principle. It treats cloud resources as software artifacts. They are versioned in Git, tested in pipelines, and deployed predictably. This methodology eradicates configuration drift and makes disaster recovery a deterministic, automated procedure.
Two tools dominate this space:
Terraform: The industry-standard, cloud-agnostic tool for declarative infrastructure provisioning. An architect uses Terraform to define the desired state of infrastructure in HCL (HashiCorp Configuration Language), enabling the creation of identical, reproducible environments across AWS, GCP, Azure, and more.
Pulumi: A modern alternative that allows engineers to define infrastructure using general-purpose programming languages like Python, TypeScript, or Go. This is a game-changer for complex logic, as it enables the use of loops, functions, classes, and unit testing frameworks from software engineering to manage cloud resources.
CI/CD and GitOps Automation
The architect designs the automated pipelines that transport code from a Git commit to a running production service securely and efficiently.
GitLab CI / GitHub Actions: These CI/CD platforms are integrated directly into the source control management systems developers use daily. An architect designs pipeline templates (
.gitlab-ci.ymlor GitHub Actions workflows) that automate building container images, running static analysis, executing unit and integration tests, and triggering deployments.ArgoCD: The leading tool for implementing GitOps. GitOps is a paradigm where the Git repository is the single source of truth for the desired state of the application and infrastructure. ArgoCD continuously reconciles the state of a Kubernetes cluster with the configurations defined in Git, automating deployments and making rollbacks as simple as a
git revert.
Observability Platforms
In a distributed system, traditional monitoring is insufficient. An architect must design a comprehensive observability stack to provide deep, actionable insights. This involves instrumenting applications to emit the "three pillars": metrics, logs, and traces. You can dig deeper into this topic with our guide on cloud-native application development.
Prometheus: The de facto open-source standard for collecting time-series metrics. It uses a pull-based model to scrape metrics endpoints from applications and infrastructure, providing the raw data for alerting and performance analysis.
Grafana: The premier visualization tool for observability data. Architects and SREs use Grafana to build real-time dashboards that correlate metrics from Prometheus, logs from Loki, and traces from Tempo, providing a unified view of system health.
OpenTelemetry (OTel): A critical, vendor-neutral CNCF project for standardizing the instrumentation of applications to generate traces, metrics, and logs. By championing OTel adoption, an architect ensures that observability data is portable, preventing vendor lock-in and future-proofing the observability stack.
An architect must also be adept at selecting the right cloud platform. While hyperscalers are common, robust decentralized solutions can offer advantages in certain scenarios. Teams exploring their options should consider powerful AWS alternatives that offer competitive pricing and unique features.
How to Hire and Vet an Elite Cloud Native Architect
In a market where true cloud native talent is scarce, hiring an architect is a strategic investment. Standard hiring processes often attract senior engineers who can operate tools but lack the strategic vision to design complex systems. To land a genuine architect, you need a more rigorous, technically-focused approach.
The pressure is on. By 2026, a staggering 95% of new digital workloads are projected to be built on cloud-native platforms, up from just 30% in 2021. This shift is why the market for these platforms is expected to rocket from $5.85 billion in 2024 to an incredible $62.72 billion by 2034. You can find more on these cloud computing statistics on Softjourn.com. You need an architect who can lead this technical transformation, not just participate in it.
Crafting a Job Description That Attracts Strategists
Your job description is your first filter. A generic list of technologies like "Kubernetes, Terraform, Prometheus" will attract tool operators. To attract an architect, frame the role around strategic impact and complex problem-solving. Focus on the why and the what, not just the how.
A Framework for a Better Job Description:
- The Mission: Start with a purpose-driven one-liner. "As our Cloud Native Architect, you will own the architectural vision and technical strategy that enables our engineering teams to ship resilient, secure, and cost-effective distributed systems at scale."
- Strategic Duties: Frame responsibilities as high-level technical challenges. Instead of "Manage Kubernetes," try "Design and evolve our container orchestration platform to support a zero-downtime, multi-region deployment strategy for critical stateful services, defining standards for security and observability."
- Key Outcomes: Define success with specific metrics. "Reduce lead time for changes by 30% through pipeline optimization" or "Decrease cloud expenditure by 20% by implementing FinOps practices and architectural redesigns for cost efficiency."
- Technical Leadership: Emphasize mentorship and governance. "You will define the architectural principles, reference implementations, and reusable patterns that guide our engineering organization, actively mentoring teams on distributed systems design and cloud native best practices."
This reframing signals that you're hiring for a designer and influencer, attracting candidates who think in terms of systems and trade-offs.
Asking Interview Questions That Reveal True Depth
Any candidate can recite definitions. To vet a top-tier architect, you must present them with realistic scenarios that force them to make and defend difficult trade-offs involving cost, security, latency, and operational complexity.
Advanced Interview Questions to Try:
- The Budget-Constrained System Design: "Design a highly available, multi-region architecture for a stateful application, like a user session store, on a strict budget. Walk me through your choice of database (e.g., managed service like DynamoDB vs. self-hosted CockroachDB on VMs). Justify how you would balance fault tolerance against operational cost and complexity."
- The Technical Debate: "Argue the pros and cons of implementing a service mesh like Istio for all east-west traffic versus relying on a simpler API gateway and client-side libraries for resilience and security. In what specific scenario is a service mesh non-negotiable? What are the hidden operational costs you'd warn the team about?"
- The Security Catastrophe: "A critical zero-day vulnerability (like Log4Shell) is announced for a library used in 50 of our microservices. Detail your immediate tactical plan (containment), mid-term plan (patching), and long-term strategic plan (prevention). How would your ideal architecture and CI/CD setup facilitate a rapid response?"
When evaluating candidates, structured interview methods like the STAR method are invaluable. For inspiration, review these 8 STAR Interview Sample Questions to help you probe past performance.
Using an Evaluation Rubric for Objective Assessment
A well-defined rubric removes subjectivity from the hiring process. It ensures every candidate is measured against the same high bar, forcing the interview panel to move beyond gut feelings to a concrete evaluation of architectural competence.
An evaluation rubric is your best defense against hiring a senior engineer for an architect's job. It codifies the strategic thinking, leadership, and business sense that define the role, making sure you assess for architectural impact, not just technical skill.
Your rubric should score candidates across several critical domains:
| Evaluation Area | 1 (Needs Development) | 3 (Proficient) | 5 (Exceptional) |
|---|---|---|---|
| System Design Depth | Offers tool-first solutions without analyzing trade-offs. | Designs logical systems but overlooks critical concerns like data consistency, failure modes, or network partitions. | Presents multiple design options, rigorously defending the chosen path with clear trade-offs across cost, latency, security, and operability. |
| Cost-Optimization Mindset | Considers cost only when prompted. Defaults to expensive managed services. | Includes cost as a design factor but lacks specific optimization strategies. | Proactively designs for cost efficiency, discussing FinOps, rightsizing, spot instance usage, and data transfer costs from the outset. |
| Security-First Principles | Treats security as a post-deployment checklist. Fails to identify common architectural vulnerabilities. | Applies basic security practices (e.g., secrets management) but overlooks deeper threats like supply chain attacks. | Integrates security into every architectural layer ("shift-left"), discussing threat modeling, principle of least privilege, and automated compliance as core design tenets. |
| Collaborative Leadership | Presents designs as rigid mandates. Struggles to explain complex technical concepts simply. | Communicates technical decisions clearly but operates primarily as an individual contributor. | Articulates complex architectural trade-offs to non-technical stakeholders and actively seeks and incorporates feedback, fostering a culture of collaborative design. |
Finding the right architect can be a significant challenge. If you need to bridge this skills gap without a lengthy hiring cycle, engaging external expertise is a powerful alternative. Our guide on hiring a cloud infrastructure consultant provides actionable advice on this model.
Augmenting Your Team with On-Demand Cloud Native Expertise

What if you could access elite cloud native architectural expertise without the months-long, high-cost process of a full-time hire? The market for true cloud native architects is incredibly competitive, marked by high salary demands and the significant risk that a bad hire could derail your technical roadmap.
An on-demand augmentation model offers a smarter alternative, providing immediate access to top-tier talent precisely when you need it. This approach bypasses the hiring bottleneck, de-risks your cloud transformation, and provides both strategic guidance and hands-on execution from day one.
The Problem with Traditional Hiring
The conventional process for acquiring architectural talent is fraught with delays. You can spend months screening candidates, conducting multi-stage interviews, and negotiating offers, all while your critical technical initiatives are stalled.
Once hired, a new architect requires a significant onboarding period to become fully productive, incurring a massive hidden cost in lost momentum. Worse, if the hire proves to be a poor fit, you are back at square one, having wasted significant time and capital. For any organization focused on velocity, this is an unacceptable drag on progress.
A Flexible Model for Immediate Impact
An on-demand model, like the one we've built at OpsMoon, flips the script. Instead of a rigid, long-term commitment, you gain flexible access to a curated pool of the world's best cloud native architects and engineers. We provide direct access to the top 0.7% of vetted global experts.
This allows you to engage an architect for the specific challenge at hand, whether it's high-level strategic planning, a well-defined project build-out, or augmenting your team's existing capacity with specialized skills.
Our flexible engagement models cover every need:
- Advisory: Access high-level strategic guidance from a seasoned architect to define your roadmap, validate your technology choices, and establish architectural best practices.
- Project-Based: Delegate an entire project, such as a Kubernetes migration or CI/CD pipeline implementation, to a dedicated expert team that manages it from design to delivery.
- Team Extension: Seamlessly embed one or more of our experts into your existing team to fill skill gaps, accelerate velocity, and transfer knowledge without HR overhead.
This flexibility allows you to scale expertise up or down in alignment with your product roadmap, ensuring continuous progress without the burden of a fixed headcount.
The core benefit here is speed and precision. You get the right expertise for the right problem, right now. It's about surgically applying top-tier talent to unlock your team's potential and hit your business goals faster.
How OpsMoon De-Risks Your Cloud Journey
Our engagement process is designed to deliver tangible value from the first conversation. It begins with a free work planning session, where we collaborate with you to understand your current state, define your goals, and co-create a strategic technical roadmap. This session alone often provides more clarity than weeks of internal meetings.
From there, our Experts Matcher technology identifies the ideal specialist for your unique technology stack, team culture, and business objectives, ensuring a precise fit. As you weigh your options, you might also find it helpful to research different DevOps outsourcing companies to see how various models compare.
To maximize value from day one, we include unique benefits in every engagement:
- Complimentary Architect Hours: We bundle free architect hours with our engineers to ensure tactical execution remains perfectly aligned with high-level architectural strategy and best practices.
- Transparent Progress Tracking: We provide real-time visibility into project progress through shared dashboards, detailed reporting, and clear, continuous communication.
- Continuous Improvement: Our experts don't just execute tasks. They proactively identify opportunities to optimize your systems for cost, security, and performance, delivering compounding value over time.
By combining elite talent with a structured, transparent process, we eliminate the guesswork and risk from your DevOps and cloud native initiatives, freeing your team to focus on its core mission: building exceptional products.
Frequently Asked Questions About the Architect Role
As the cloud native architect role becomes a fixture in engineering organizations, several key questions frequently arise. These questions highlight the critical distinctions between this strategic function and other senior technical roles. Clarity here is essential for both hiring managers defining the role and engineers aspiring to it.
What Is the Difference Between a DevOps Engineer and a Cloud Native Architect?
The fundamental difference lies in scope and focus: the architect defines the "what and why," while the engineer executes the "how." A DevOps Engineer is the hands-on implementer. They are masters of the "how"—building and maintaining CI/CD pipelines, writing automation scripts, and ensuring the day-to-day operational health of the platform.
A cloud native architect operates at the level of "what and why." They design the system's blueprint, making the strategic technical decisions that the DevOps engineer will then implement. The architect determines the microservice boundaries, selects the inter-service communication patterns (e.g., synchronous vs. asynchronous), defines the data consistency model, and sets the organization-wide standards for reliability and security.
Think of it like this: the architect designs the city's entire power grid, water systems, and road network (the blueprint). The DevOps engineer is the specialized construction lead who actually builds, connects, and maintains that infrastructure based on the plan.
Should a Cloud Native Architect Still Write Code?
Yes, absolutely. An architect who doesn't write code becomes detached from reality and loses credibility. While they may not be shipping product features daily, they must remain hands-on by coding in specific, high-leverage areas.
Effective architects regularly write and review code in these domains:
- Infrastructure as Code (IaC): Actively authoring and reviewing modules in Terraform or Pulumi to define and govern complex, reusable infrastructure components.
- Proof-of-Concepts (PoCs): Building small, working prototypes to evaluate new technologies (e.g., a new service mesh, vector database, or observability backend) and de-risk their adoption by testing performance, integration, and operational overhead.
- Automation Scripting: Writing scripts for architectural governance, such as tools that scan IaC for policy violations or scripts that analyze cloud cost and usage data.
- Reusable Libraries and Frameworks: Contributing to shared libraries that enforce architectural standards, such as standardized logging, tracing instrumentation, or resilience patterns (e.g., circuit breakers).
If an architect is not involved at this level, their designs become theoretical and disconnected from the practical challenges faced by the engineering team.
Can a Solutions Architect from AWS or GCP Fill This Role?
Not directly, and this is a critical distinction to understand. A Solutions Architect from a cloud provider (AWS, GCP, Azure) is an expert in their employer's product portfolio. Their primary function is to map customer problems to their platform's specific services. It's a sales and advisory function, not a pure architectural one.
A true cloud native architect is vendor-agnostic by default. Their allegiance is to core architectural principles like loose coupling, observability, and portability, not to a specific vendor's ecosystem.
For instance, when faced with a messaging requirement, a vendor SA will almost certainly propose their platform's managed queue service (e.g., SQS or Pub/Sub). A cloud native architect will first analyze the system's specific needs (e.g., at-least-once vs. exactly-once delivery, message ordering guarantees, throughput requirements) and then select the best tool. This could be an open-source option like RabbitMQ or NATS, a managed service, or a different architectural pattern entirely. They prioritize architectural integrity and avoiding vendor lock-in.
How Do You Measure the ROI of a Cloud Native Architect?
The impact of a cloud native architect is not measured in lines of code or features shipped. Their return on investment (ROI) is reflected in the velocity, reliability, and efficiency of the entire engineering organization. Their value is quantified through improvements in key engineering and business metrics.
Success is directly visible in these areas:
- Developer Velocity: Are teams able to ship features to production faster and more safely? Measure this with DORA metrics like Lead Time for Changes (from commit to deploy) and Deployment Frequency.
- System Reliability: Is the system more resilient to failures? Measure this with Mean Time To Recovery (MTTR)—how quickly the system recovers from an outage—and Service Level Objective (SLO) attainment.
- Operational Efficiency: Is the cloud spend more efficient? Track metrics like cloud cost per customer or cost per transaction. An architect's design choices have a direct and significant impact on cloud bills.
- Scalability and Performance: Does the system handle load spikes gracefully and automatically? Monitor metrics like p95/p99 API response times under load and the frequency of automated scaling events versus manual interventions.
Ultimately, the architect's ROI is the organization's enhanced ability to ship better software faster, more reliably, and at a sustainable cost.
Ready to accelerate your cloud native journey without the risk of a bad hire? OpsMoon connects you with the top 0.7% of vetted global experts who can provide strategic guidance, execute on projects, or augment your existing team. Start with a free work planning session to build your roadmap today. Learn more at opsmoon.com.
Leave a Reply