If you're a CTO or engineering leader, you've likely encountered the term "SOC compliant," especially when pursuing enterprise contracts. But what does it actually mean from a technical and operational standpoint?
Let's cut through the noise. Becoming “SOC compliant” means you’ve had a licensed CPA firm audit your internal controls—the specific policies, procedures, and technical configurations that govern your systems—and formally attest that you’re effectively protecting customer data. It’s not a one-and-done certificate; it’s a rigorous audit report that details the design and operational effectiveness of your control environment.
Think of it as a trust primitive. A powerful one. For modern tech companies, it’s often the key that unlocks those enterprise contracts you’re chasing.
Understanding the Foundation of SOC Compliance
In B2B, especially for SaaS and cloud services, trust is a non-negotiable prerequisite. When a large organization entrusts you with their data, they require verifiable, objective proof that your systems are secure and your processes are sound. A SOC (System and Organization Controls) report is that proof.
It’s the equivalent of a detailed penetration test and architectural review combined, conducted by a certified third party. It gives potential customers a deep, technical look under the hood to validate that your security posture is not just a claim but a demonstrable reality. Without it, your service will likely be filtered out during the vendor security review phase of any serious procurement process.

Not a Law, but a Market Requirement
Here’s a critical distinction: SOC is not a government regulation like GDPR or HIPAA. You are not legally compelled to obtain a SOC report. Its authority stems from something far more immediate: market demand.
The framework was developed by the American Institute of Certified Public Accountants (AICPA) to create a standardized methodology for service organizations to report on their internal controls. It rapidly became the de facto standard for demonstrating due care.
This is especially true in DevOps and SaaS. As other regulations tighten, the market’s reliance on attestation frameworks like SOC is increasing. For instance, 78% of CISOs are expected to agree that regulations like GDPR effectively reduce cyber risks by 2026, a significant increase from 61% in 2024. For technical leaders, the message is clear: a SOC 2 attestation is no longer a nice-to-have. It’s a core component of a defensible security program. You can dig into more data on these trends in this market report.
It's crucial to understand that a SOC report isn't a simple pass/fail grade. It’s a detailed opinion from a CPA firm about your control environment. It describes how your controls are designed and whether they operate effectively, and it will even call out any exceptions (i.e., control failures) found during the audit.
The Three Flavors of SOC Reports
SOC isn’t a single report; it's a family of reports, and selecting the correct one is a critical decision. A misstep here results in wasted capital and engineering cycles on an attestation that fails to meet customer requirements.
To make it simple, here's a quick breakdown of the three main types.
Quick Guide to SOC Report Types
| Report Type | Primary Focus | Target Audience | Common Use Case |
|---|---|---|---|
| SOC 1 | Internal Controls over Financial Reporting (ICFR) | Your customers' finance/audit teams | You're a payroll processor, billing service, or your platform could impact a client's financials. |
| SOC 2 | Security, Availability, Processing Integrity, Confidentiality, and Privacy | Your customers' security/tech teams | You're a SaaS, PaaS, or IaaS provider handling any kind of sensitive customer data. |
| SOC 3 | High-level summary of the SOC 2 findings | General public, marketing purposes | You need a "trust seal" for your website, but it's not detailed enough for vendor reviews. |
For most tech companies, SOC 2 is the one that matters. It's built around the five Trust Services Criteria and gives your customers' security and engineering teams the deep technical assurance they need to approve your service. SOC 1 is for a specific financial niche, and SOC 3 is a public-facing derivative of a SOC 2, lacking the necessary technical detail for vendor due diligence.
Choosing Your Compliance Path: SOC 1 vs SOC 2 vs SOC 3
Picking the right SOC report isn't just a compliance task. It's a strategic decision that directly impacts your sales velocity and GTM strategy.
A mistake here means wasted engineering cycles and a final report that doesn't satisfy your target customers' due diligence requirements. For most technology companies, the decision point is between SOC 1 and SOC 2. Understanding the technical divergence is critical.
Think of it as selecting the right diagnostic tool. A SOC 1 report is a precision instrument, laser-focused on Internal Control over Financial Reporting (ICFR). If your service's logic or data processing impacts a client's financial statements—for example, as a payroll platform, revenue recognition engine, or billing system—their external auditors will demand a SOC 1 report to ensure your system's integrity doesn't compromise their financial audit.
But for the vast majority of SaaS, PaaS, and IaaS providers, the conversation begins and ends with SOC 2.
Deep Dive into SOC 2: The Gold Standard for Tech
A SOC 2 report answers a much broader, more fundamental question: "Can I trust this vendor's systems and processes to protect my sensitive data?"
Instead of focusing on financial reporting, SOC 2 evaluates your organization against the AICPA's five Trust Services Criteria (TSC). These criteria provide a flexible yet rigorous framework for demonstrating security and operational resilience.
The Security criterion (also known as the Common Criteria) is the mandatory foundation. The other four are optional and should be selected based on explicit service commitments and customer contractual requirements. Over-scoping by including unnecessary criteria leads to increased audit costs and a larger surface area for potential findings.
Here is a technical breakdown of what each criterion covers.
SOC 2 Trust Services Criteria Explained
| Trust Service Criterion | Core Objective | Example DevOps Control |
|---|---|---|
| Security (Common Criteria) | Protect the system against unauthorized access (both logical and physical) to prevent misuse, data theft, or abuse. | Implement role-based access control (RBAC) in Kubernetes and enforce MFA for all production environment access. |
| Availability | Ensure the system is available for operation and use as committed or agreed upon in your SLAs. | Use multi-AZ deployments for critical services and have a tested disaster recovery plan with defined RTO/RPO. |
| Processing Integrity | Verify that system processing is complete, valid, accurate, timely, and authorized. | Implement input validation checks in your CI/CD pipeline and use checksums to verify data integrity during transfers. |
| Confidentiality | Protect information designated as "confidential" from unauthorized disclosure. | Enforce data encryption at rest (e.g., EBS volume encryption) and in transit (TLS 1.2+), with strict access controls on secrets. |
| Privacy | Ensure personal information (PII) is collected, used, retained, and disposed of in conformity with your privacy notice. | Automate data retention and deletion policies. Use data masking techniques in non-production environments. |
Each of these criteria requires you to prove that you have appropriate controls designed and implemented, and, more importantly, that they are operating effectively.
Type I vs. Type II: Why It Matters
After selecting your report type and criteria, you face another decision: Type I versus Type II. This is a frequent point of confusion, but the distinction has significant business implications.
A SOC 2 Type I report is a point-in-time assessment. The auditor attests only to the suitability of the design of your controls at a specific moment. It’s a reasonable first step but offers no assurance that your controls are actually being followed.
A SOC 2 Type II, on the other hand, is a longitudinal study.
The auditor examines evidence to attest that your controls were operating effectively over a sustained period, typically 3 to 12 months. Any mature enterprise buyer will require a Type II report. It is the non-negotiable standard because it provides substantive assurance that your security program is a living process, not just a theoretical design.
SOC 3: The Public-Facing Handshake
Finally, there’s the SOC 3 report. A SOC 3 is a high-level, public-facing summary of a SOC 2 Type II audit.
It provides a general attestation that the criteria were met but omits the detailed descriptions of your controls, the auditor's tests, and the test results. While useful for marketing—a "trust seal" for your website—it lacks the technical depth required for a vendor security review. Your technical buyers will always request the full SOC 2 report under NDA.
The demand for these reports is exploding. The global market for SOC Reporting Services was valued at $5.392 billion in 2024 and is on track to hit $10.47 billion by 2030. This growth is driven by the escalating need for service providers to build verifiable trust in an environment of increasing cyber threats.
For DevOps teams, achieving SOC 2 compliance is no longer a discretionary security initiative. It is a direct enabler of B2B revenue. You can dig into more data on the SOC reporting services market to see just how fast this space is growing.
Your Step-By-Step Technical Audit Roadmap
Undertaking a SOC audit can feel like preparing for a high-stakes technical examination. However, by approaching it as a structured engineering project rather than a compliance mandate, it becomes a defined and manageable process.
I've broken down the entire journey into six clear, actionable phases. This is your project plan. Each step builds on the last, systematically moving your organization from a state of audit-unawareness to full readiness, providing technical teams with the necessary clarity.
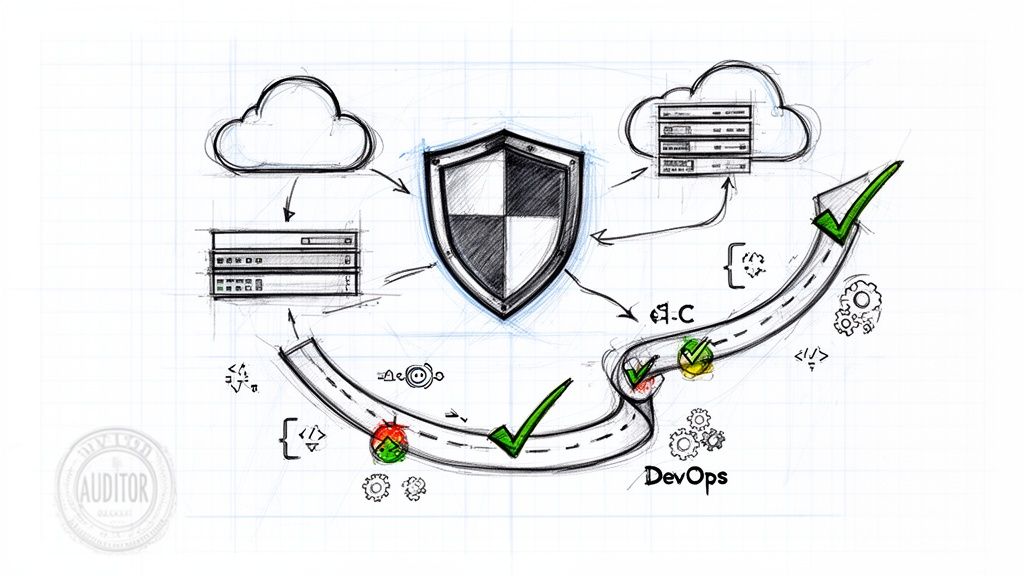
This flow shows how the different SOC reports relate to one another, from the financial-focused SOC 1, to the security-deep SOC 2, and its public-facing summary, SOC 3.

The key takeaway here is that SOC 2 is usually the core technical effort. The other reports, like SOC 3, are often just summaries derived from it.
Step 1: Define Scope and Choose Criteria
First, you must precisely define the audit's scope. This is not a time for ambiguity. You need to map every system component, data repository, code pipeline, and key personnel involved in the delivery of your service. This "system boundary" is critical.
With that boundary defined, you select your Trust Services Criteria (TSC). Security is mandatory. The inclusion of others, like Availability or Confidentiality, must be driven by your contractual commitments and SLAs. A common error is over-scoping, which needlessly increases audit costs and engineering effort. Be precise and defensible in your choices.
Step 2: Conduct a Readiness Assessment
Before engaging an audit firm, you must perform a self-audit. A readiness assessment is a mock audit designed to identify control gaps before they become official findings in your report. This is the single most important step for avoiding a qualified or, in a worst-case scenario, an adverse opinion.
This can be conducted internally if you possess the requisite GRC expertise, but most organizations engage a third-party consultant for an objective analysis. The deliverable should be a detailed gap analysis report, which serves as a prioritized backlog for your engineering team.
Step 3: Execute Gap Remediation
This is where your engineering team executes. The readiness assessment provides the remediation backlog. The objective is to close identified gaps through a combination of technical implementation and process formalization.
This is where the real work happens:
- Implementing Controls: This ranges from configuring MFA and granular IAM roles to enabling at-rest encryption and implementing new alerting rules in your observability platform.
- Documenting Processes: Formalizing policies for change management, incident response, and logical access review is as critical as the technical implementation. The documentation serves as the "what" and the technical controls are the "how."
- Automating Evidence: Whenever possible, automate the collection of audit evidence. A mature DevSecOps pipeline is a significant force multiplier, converting much of the audit from manual data gathering to automated reporting.
Step 4: Select a Reputable CPA Firm
Your auditor is a crucial partner in this process. It’s vital to select a CPA firm with demonstrable expertise in auditing cloud-native technology stacks and companies of your scale. You need auditors who understand environments like AWS, Kubernetes, and modern CI/CD tooling, not just legacy on-premise systems.
Solicit proposals from multiple firms and request references from companies with similar technical profiles. Their understanding of your stack will directly influence the efficiency and relevance of the audit.
Step 5: Navigate Audit Fieldwork
This is the execution phase of the audit. For a SOC 2 Type II, the auditors will collect and test evidence to verify that your controls operated effectively throughout the review period, which is typically 6 or 12 months.
Expect to provide a mountain of technical evidence. This includes git commit histories showing peer reviews, screenshots of IAM role configurations, CI/CD pipeline logs demonstrating approval gates, and reports from vulnerability scanners.
This is where automation delivers a massive ROI. A well-instrumented environment makes evidence collection a programmatic task rather than a frantic, manual fire drill.
Step 6: Receive and Interpret Your Report
Finally, the CPA firm issues the SOC report. It contains their formal opinion, a detailed management assertion describing your system, the auditor's description of tests of controls, and the results of those tests.
If minor control failures were identified, they will be noted as "exceptions." Read the report meticulously, develop a remediation plan for any exceptions, and prepare for the next audit cycle. This report is a critical sales asset, so be prepared to share it with prospects under an NDA.
Essential DevOps Controls and Evidence for SOC 2

For an engineering team, understanding what is SOC compliant is about translating abstract security principles into concrete, automated controls embedded within daily workflows.
A SOC 2 audit is not a checklist exercise. It's about demonstrating that your DevOps practices consistently and verifiably deliver on your security and operational commitments.
Auditors require objective evidence, preferably generated directly by your tooling, not just policy documents. A modern, cloud-native stack is a compliance superpower. By instrumenting your environment correctly, you can transform the arduous task of evidence gathering into a series of automated reports.
Let's dissect the essential DevOps controls and the specific, "auditor-friendly" evidence required for each.
Access Control and Identity Management
This domain focuses on enforcing the principle of least privilege. In a cloud-native architecture, this extends far beyond username/password credentials.
Your objective is to prove that access is systematically provisioned, reviewed, and de-provisioned. Auditors will scrutinize evidence demonstrating strong authentication and a "default deny" permissions model.
- Control Example: Enforce Multi-Factor Authentication (MFA) for all users accessing production systems and sensitive third-party services (e.g., cloud consoles, GitHub, Okta).
- Evidence: A screenshot from your Identity Provider (IdP) like Okta or Azure AD demonstrating a globally enforced MFA policy. An AWS IAM credential report confirming MFA is active for all relevant users is also excellent evidence.
- Control Example: Utilize Role-Based Access Control (RBAC) in Kubernetes to define granular permissions for users and service accounts. In your cloud environment, use strict IAM roles to grant temporary, scoped-down credentials instead of long-lived static keys.
- Evidence: The YAML definition for a Kubernetes Role or ClusterRole, paired with a RoleBinding that associates it with a specific user or group. For cloud evidence, the JSON policy document of an AWS IAM role that explicitly shows its limited permissions (
Action,Resource,Condition) is exactly what an auditor needs.
Change Management and CI/CD Pipelines
Change management is a core focus for any auditor. They require assurance that every modification to a production system is authorized, tested, and documented. For a DevOps team, this maps directly to the CI/CD pipeline.
A well-architected pipeline is your strongest control, creating an immutable, automated audit trail for every change. To dig deeper into setting up a compliant system, check out our guide on SOC 2 requirements.
The goal is to prove that no single engineer can unilaterally deploy code to production. Your pipeline must have automated, non-bypassable checks and balances. This prevents unauthorized or untested changes from reaching production.
Here’s how to translate pipeline stages into auditable controls:
- Control Example: Mandate that all code changes are submitted via a pull request (PR) that requires at least one peer review and approval before merging to the main branch.
- Evidence: A direct link or screenshot from GitHub/GitLab showing a merged PR with its "approved" status, the associated commits, and links to the corresponding Jira ticket that documents the business justification.
- Control Example: Implement automated approval gates in your CI/CD pipeline (e.g., using Jenkins, GitLab CI, or CircleCI) that halt a deployment to production pending explicit approval from a designated approver or group.
- Evidence: A screenshot of your pipeline-as-code definition (e.g.,
Jenkinsfile,.gitlab-ci.yml) showing the manual approval stage. Deployment logs from a tool like Spinnaker or Argo CD that record the approver's identity and timestamp are also ideal.
System Operations and Monitoring
This section concerns how you monitor system health, manage incidents, and maintain operational stability. Your observability stack (e.g., Prometheus, Grafana, Datadog) is the primary source of evidence here.
You must prove that you can detect and respond to anomalies and incidents in a timely and systematic manner. It’s insufficient to simply have monitoring tools; you need documented procedures that demonstrate how your team uses them.
- Control Example: Implement automated monitoring and alerting on key service-level indicators (SLIs) such as latency, error rate, throughput, and saturation.
- Evidence: A Grafana or Datadog dashboard visualizing these metrics over time. The configuration files for alerting rules (e.g., from Prometheus's Alertmanager or PagerDuty) that define thresholds and notification channels are primary evidence.
- Control Example: Maintain a formal, documented Incident Response (IR) plan. This plan must detail the phases of incident management: identification, containment, eradication, recovery, and post-mortem.
- Evidence: The IR plan document itself is a starting point. More compelling evidence includes post-incident review reports from past incidents demonstrating that you followed the plan. Jira tickets used to coordinate the response are also excellent evidentiary artifacts.
Security and Vulnerability Management
Finally, auditors require proof that you are proactively identifying and remediating security vulnerabilities across your application code, container images, and infrastructure. As you plan your technical audit, getting a handle on the top 10 internal controls best practices can seriously beef up your compliance game.
Regulatory pressure is also forcing everyone's hand. It's predicted that by 2026, 58% of organizations will run four or more audits a year, with some big companies doing more than six. And while 78% of CISOs agree that regulations help reduce risk, 69% are struggling to keep up with vendor compliance. This audit treadmill makes continuous, automated evidence collection non-negotiable—and it's a core strength of any mature DevOps practice. You can find more on these trends in this SOC as a Service Market report.
- Control Example: Integrate Static Application Security Testing (SAST) tools like Snyk or SonarQube directly into your CI pipeline to scan for code vulnerabilities on every commit or build.
- Evidence: Pipeline logs showing the successful execution of a SAST scan. The actual reports from the tool listing identified vulnerabilities (with CVEs) and their severity levels are crucial.
- Control Example: Automate vulnerability scanning for all container images stored in your registry (e.g., AWS ECR, Docker Hub, JFrog Artifactory).
- Evidence: Reports from a scanner like Trivy or Clair that provide a manifest of vulnerabilities found in a specific image hash. You must also provide evidence that your process prevents images with critical vulnerabilities from being deployed.
Alright, let's talk about what a SOC report will actually cost you in time and money. Knowing what SOC compliance is and needing to pay for it are two very different things. For any technical leader, getting this forecast right is the key to setting sane expectations with your board, your sales team, and everyone in between.
This isn't just another line item on your budget. Think of it as a major strategic investment in building trust with your customers. The total cost isn't one single bill; it's a mix of your team's time, outside help, and often, new tools.
Breaking Down the Core Cost Areas
When you start pulling apart a SOC 2 initiative, you'll find the costs fall into three main buckets.
First up, and usually the biggest chunk, is Readiness and Remediation. This is all the prep work you do before the auditors even show up. It’s where you find all the gaps in your security posture and, more importantly, fix them.
This phase can include a few different expenses:
- Consulting Fees: Lots of companies bring in an outside expert for a readiness assessment. It gives you an unbiased look at where you stand. Expect this to run anywhere from $10,000 to $30,000+, depending on how complex your setup is.
- New Security Tools: Your assessment will almost certainly uncover a need for new software. This could be anything from an identity provider (IdP) and vulnerability scanners to endpoint detection and response (EDR) agents for all your employee laptops.
- Critical Engineering Hours: This is the big one that often gets missed. It’s the internal cost of your own team's time. Your engineers are going to be busy—implementing new controls, documenting everything, and sometimes re-architecting systems to tick all the SOC 2 boxes. This is easily the most underestimated "cost" of the whole project.
The second category is the Direct Audit Fee. This is what you actually pay the CPA firm to come in and do the attestation. For a first-time SOC 2 Type II audit, you can expect to pay between $15,000 and $60,000+. The final number really depends on the scope—how many systems you’re including and which of the Trust Services Criteria you've chosen to pursue.
Finally, don't forget about Ongoing Maintenance. SOC compliance isn't a one-and-done deal; it's a program you have to keep running. You’ll need to budget for the annual renewal audit, which is usually a bit cheaper than the first one but still a real cost. Plus, you'll have recurring subscription fees for any compliance automation platforms or security tools you put in place.
A Realistic Timeline for Your First Audit
A classic mistake is thinking you can knock this out in a quarter. A first-time SOC 2 Type II audit is a marathon, not a sprint. For most startups and mid-sized companies, you’re looking at a journey of 9 to 15 months from start to finish.
Here’s what that timeline typically looks like:
- Phase 1: Readiness & Remediation (3-9 Months): This is the long haul. You'll do the readiness assessment, figure out your biggest gaps, and have your engineers get to work implementing all the technical and process controls.
- Phase 2: Observation Period (3-6 Months): For a Type II report, the auditor needs to see your controls actually working over a period of time. This "review" or observation window is usually at least three months, but it can be longer.
- Phase 3: Audit Fieldwork & Reporting (1-3 Months): Once the observation period is over, the auditors roll in. They start collecting evidence, interviewing your team, and testing your controls. After that, they’ll write up the final report.
It's absolutely crucial to communicate this long-term timeline to your board and sales team. Promising a SOC 2 report to a major prospect in three months is a recipe for disaster if you haven't even started your readiness assessment.
Failing to get your engineering team bought in, scoping the audit too broadly (or too narrowly), or just treating compliance like a checkbox exercise are all common ways to derail the project and blow up your budget. Plan for these financial and time commitments from day one—it's the only way to get through this successfully.
Accelerating Your SOC Compliance Journey
Let's be honest: the SOC compliance path can feel like a slow, painful grind. It’s a resource hog, especially for teams that are already stretched thin.
But achieving attestation doesn't have to mean derailing your product roadmap for a year or building a dedicated internal GRC team. With a strategic approach, you can leverage specialized DevOps expertise to accelerate the entire process.
Think of it like bringing in a pit crew for a race car. You're not building the car from scratch. You're engaging specialists who know precisely how to tune the engine, reinforce the chassis, and pass technical inspection—efficiently.
Surgical Strikes with DevOps Experts
A dedicated DevOps partner begins by mapping your existing infrastructure and operational processes directly to the specific SOC 2 controls. This is not a generic audit; it's a focused technical analysis designed to identify the delta between your current state and an audit-ready state.
This is where specialized expertise becomes a force multiplier, particularly with modern technology stacks. Engineers fluent in secure, compliant infrastructure-as-code (IaC) using tools like Terraform, Kubernetes, and automated CI/CD pipelines can apply targeted fixes. They don't just produce a report with recommendations; they actively implement the required controls within your environment.
This model yields several key advantages:
- Targeted Remediation: Instead of a resource-intensive "boil the ocean" approach, experts concentrate on the specific controls required to pass the audit, minimizing wasted engineering effort.
- Infrastructure as Code (IaC): Using tools like Terraform ensures your compliant infrastructure is declarative, version-controlled, repeatable, and inherently auditable. The configuration is the documentation.
- Automated Evidence Collection: Experts can configure your CI/CD pipelines and monitoring systems to automatically generate the evidentiary artifacts auditors require, converting a tedious manual task into an automated reporting function.
If you want to see how specialized platforms can help with this, you can explore Passflow's services to get a feel for what’s out there.
From Project to Operational Capability
By partnering with a dedicated firm, SOC compliance transitions from a daunting, one-off project into a manageable, continuous operational function. With access to expert architects and a clear, shared view of progress, the remediation roadmap remains on schedule.
The ultimate goal is to embed compliance directly into your daily operations. When security controls are automated within your CI/CD pipeline and your infrastructure is managed via code, compliance becomes a natural byproduct of good engineering, not a separate task.
This model allows your internal team to maintain focus on core product development. The compliance work proceeds in parallel, guided by specialists who have navigated the process hundreds of times. It makes the journey to becoming SOC compliant significantly faster and more cost-effective.
Curious about the first steps? You can learn more about how to get SOC 2 certification in our detailed guide.
Common Questions About SOC Compliance
Even with a solid plan, a few nagging questions about SOC compliance always seem to pop up for technical leaders. Getting straight answers is the only way to build a real strategy and explain it to the rest of the business.
Let's tackle the ones I hear most often.
Is SOC 2 Compliance Mandatory?
No, SOC 2 is not a statutory or regulatory requirement. You will not receive a government fine for not possessing a SOC 2 report.
However, in the B2B SaaS market, it functions as a powerful commercial mandate. Mature enterprise customers have vendor risk management (VRM) policies that will automatically disqualify any vendor handling their data without a current SOC 2 Type II report.
So, while not legally mandated, foregoing SOC 2 is a strategic decision to self-select out of the enterprise market segment. It is the key that unlocks access to larger, more security-conscious customers.
How Does SOC 2 Differ From ISO 27001?
Both are premier information security standards, but their frameworks and outputs are fundamentally different.
- ISO 27001 is a certification. An organization implements a formal Information Security Management System (ISMS) that must conform to a rigid, prescriptive set of controls defined in the standard (Annex A). It is a globally recognized standard, particularly dominant in Europe and Asia.
- SOC 2 is an attestation. The organization defines its own controls to meet the flexible objectives of the Trust Services Criteria (TSC). A CPA firm then attests to the design and/or operating effectiveness of those specific controls. This framework is the predominant standard in North America.
The key difference is flexibility versus prescription. SOC 2 allows you to tailor controls to your specific technology stack and business processes, whereas ISO 27001 requires adherence to a predefined management system framework. Many global companies ultimately obtain both to satisfy diverse customer requirements.
How Long Is a SOC 2 Report Valid?
This is a common point of confusion. A SOC 2 report is a historical document—it provides an opinion on a past period of observation. Therefore, it technically does not "expire."
However, its commercial relevance diminishes rapidly. Virtually all customers and prospects will consider a report that is more than 12 months old to be stale and will require a more recent one.
This practical reality transforms SOC compliance into a continuous program, not a one-time project. You must undergo an annual audit to maintain a current attestation and demonstrate an ongoing commitment to your control environment.
Ready to stop seeing SOC compliance as a roadblock and start using it as a competitive advantage? OpsMoon connects you with the top 0.7% of remote DevOps engineers who specialize in building secure, auditable infrastructure. Our experts can accelerate your readiness, implement required controls, and help you achieve compliance faster, all while your team stays focused on your product.
Leave a Reply